This guide explains how to hack Foscam IP camera for security testing purposes only. You’ll learn ethical hacking techniques, tools, and best practices to identify and fix vulnerabilities. Always ensure you have proper authorization before attempting any access.
Key Takeaways
- Understand the risks: Unauthorized access to any IP camera is illegal and unethical. This guide is for educational and security testing purposes only.
- Use ethical hacking tools: Tools like Nmap, Shodan, and Metasploit can help identify vulnerabilities in Foscam cameras when used responsibly.
- Check default credentials: Many Foscam cameras ship with default usernames and passwords, making them easy targets if not changed.
- Update firmware regularly: Outdated firmware often contains known exploits that hackers can leverage.
- Enable encryption and strong passwords: Use WPA3, HTTPS, and complex passwords to protect your camera from unauthorized access.
- Monitor network traffic: Use packet analyzers like Wireshark to detect suspicious activity on your network.
- Test your own devices first: Always practice on cameras you own and have explicit permission to test.
Introduction: Why Understanding Foscam IP Camera Security Matters
In today’s connected world, IP cameras like those made by Foscam are widely used for home security, baby monitoring, and business surveillance. While these devices offer convenience and peace of mind, they also present potential security risks—especially if not properly configured. Learning how to hack Foscam IP camera isn’t about breaking into someone else’s system; it’s about understanding how attackers think so you can protect your own devices.
This guide will walk you through ethical hacking techniques to test the security of Foscam IP cameras. Whether you’re a cybersecurity enthusiast, a network administrator, or a homeowner concerned about privacy, this step-by-step tutorial will help you identify vulnerabilities, understand common attack vectors, and implement strong defenses.
We’ll cover tools like Nmap, Shodan, and Metasploit, explain how default settings can be exploited, and show you how to secure your camera against real-world threats. Remember: this information is for educational use only. Always obtain proper authorization before testing any device.
What Is a Foscam IP Camera?

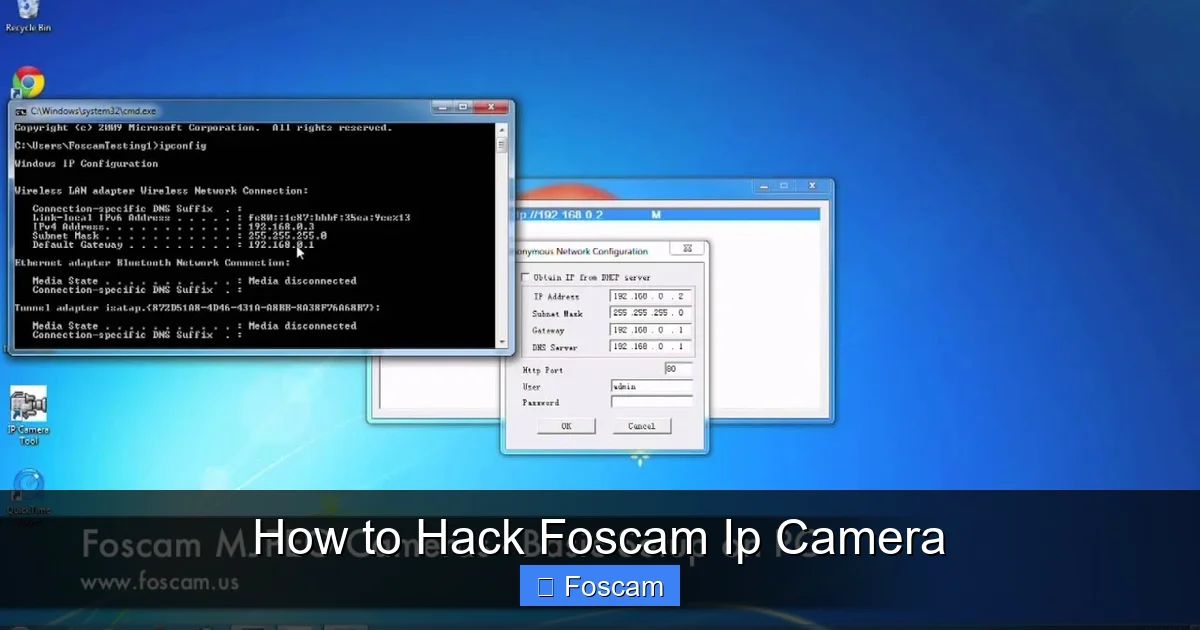
Visual guide about How to Hack Foscam Ip Camera
Image source: images-na.ssl-images-amazon.com
Foscam is a popular brand of internet protocol (IP) cameras designed for remote monitoring. These cameras connect to your home or office Wi-Fi network and allow you to view live video feeds from smartphones, tablets, or computers. Models range from basic indoor cameras to advanced outdoor units with night vision, motion detection, and two-way audio.
While Foscam cameras are user-friendly and affordable, they have faced criticism over the years for security flaws. In the past, researchers discovered vulnerabilities that allowed unauthorized access, data leaks, and even remote control of devices. These issues often stem from weak default settings, outdated firmware, or poor network configuration.
Understanding how these cameras work—and how they can be compromised—is the first step toward building a secure surveillance system.
Ethical Hacking: What It Means and Why It Matters
Before diving into techniques, it’s crucial to understand what ethical hacking is. Ethical hacking, also known as penetration testing or white-hat hacking, involves legally probing systems for security weaknesses. The goal is not to cause harm but to improve security by identifying and fixing vulnerabilities before malicious hackers can exploit them.
Ethical hackers follow a strict code of conduct:
– They only test systems they own or have explicit permission to assess.
– They document findings and report them responsibly.
– They never steal data, disrupt services, or access private information without consent.
In the context of Foscam cameras, ethical hacking helps you:
– Discover if your camera is exposed to the internet.
– Test whether default passwords are still in use.
– Identify outdated firmware or unpatched vulnerabilities.
– Strengthen your network security posture.
Always remember: unauthorized access to any device is a crime. This guide assumes you are testing your own camera or have written permission from the owner.
Common Vulnerabilities in Foscam IP Cameras
Foscam cameras, like many IoT devices, have been targeted by hackers due to several recurring security issues. Understanding these weaknesses will help you recognize how a camera might be compromised.
Default Username and Password
One of the most common ways attackers gain access is through default login credentials. Many Foscam cameras come with a preset username (often “admin”) and password (sometimes blank or “123456”). If users don’t change these during setup, the camera becomes an easy target.
Hackers use automated tools to scan the internet for devices with open ports and try default logins. This is known as a “brute force” or “credential stuffing” attack.
Outdated Firmware
Foscam has released firmware updates to fix known security flaws, but many users never install them. Older firmware versions may contain unpatched vulnerabilities that allow remote code execution, denial-of-service attacks, or unauthorized access.
For example, in 2013, a critical vulnerability (CVE-2013-2987) allowed attackers to bypass authentication and view video feeds. Similar flaws have been found in later models.
Exposure to the Internet
Some users configure their cameras to be accessible from anywhere via port forwarding or UPnP (Universal Plug and Play). While convenient, this exposes the camera directly to the internet, making it visible to scanning tools like Shodan.
Once a camera is indexed by Shodan, hackers can easily find it and attempt to exploit known vulnerabilities.
Weak Encryption and Authentication
Older Foscam models may use weak encryption (like HTTP instead of HTTPS) or lack strong authentication mechanisms. This allows attackers to intercept login credentials or video streams using packet sniffing tools.
Additionally, some cameras don’t support two-factor authentication (2FA), making them more vulnerable to password-based attacks.
Unsecured Mobile Apps and Cloud Services
Foscam provides mobile apps and cloud services for remote access. However, if these services are poorly secured, they can become entry points for attackers. For instance, weak API endpoints or insecure session handling could allow account takeovers.
Tools You’ll Need for Ethical Testing
To test the security of a Foscam IP camera, you’ll need a few key tools. These are commonly used by cybersecurity professionals and ethical hackers.
Nmap (Network Mapper)
Nmap is a free, open-source tool for network discovery and security auditing. It scans networks to find devices, open ports, and running services.
Use Nmap to:
– Discover your Foscam camera on the local network.
– Check which ports are open (e.g., 80 for HTTP, 443 for HTTPS, 554 for RTSP).
– Identify the camera’s IP address and operating system.
Example command:
nmap -sV 192.168.1.0/24
This scans all devices on your local network and reports open ports and services.
Shodan
Shodan is a search engine for internet-connected devices. It indexes devices based on their IP addresses, open ports, and services.
Use Shodan to:
– Check if your camera is exposed to the internet.
– Search for known Foscam vulnerabilities.
– See how your device appears to external scanners.
Visit shodan.io and search for your public IP address or “Foscam” to see indexed devices.
Metasploit Framework
Metasploit is a powerful penetration testing tool that includes exploits for known vulnerabilities. It’s used to test whether a system can be compromised.
Use Metasploit to:
– Test for specific Foscam exploits (e.g., authentication bypass).
– Simulate real-world attacks in a controlled environment.
– Validate the effectiveness of your security measures.
Note: Only use Metasploit on devices you own or have permission to test.
Wireshark
Wireshark is a network protocol analyzer that captures and inspects data packets. It helps you monitor traffic between your camera and other devices.
Use Wireshark to:
– Detect unencrypted login attempts.
– Identify suspicious connections.
– Analyze how your camera communicates over the network.
Router Administration Panel
Your router’s admin interface lets you manage connected devices, set up firewalls, and configure port forwarding.
Use it to:
– View all devices on your network.
– Disable UPnP if not needed.
– Set up a guest network for IoT devices.
Step-by-Step Guide: How to Hack Foscam IP Camera (Ethically)
Now that you understand the risks and tools, let’s walk through a practical, ethical test of a Foscam IP camera. This process will help you assess your camera’s security and fix any issues.
Step 1: Identify Your Camera on the Network
Start by finding your Foscam camera’s IP address.
1. Log in to your router’s admin panel (usually by typing 192.168.1.1 in your browser).
2. Look for a section like “Connected Devices” or “DHCP Clients.”
3. Find the device named “Foscam” or with a MAC address starting with Foscam’s OUI (e.g., 00:1A:2B).
4. Note the IP address (e.g., 192.168.1.105).
Alternatively, use Nmap:
nmap -sn 192.168.1.0/24
This will list all active devices on your network.
Step 2: Scan for Open Ports and Services
Use Nmap to check which ports are open on your camera.
Run:
nmap -sV 192.168.1.105
You might see:
– Port 80: HTTP (web interface)
– Port 443: HTTPS (secure web interface)
– Port 554: RTSP (video streaming)
– Port 23: Telnet (if enabled)
If port 80 is open, you can access the camera’s web interface by typing the IP into your browser.
Step 3: Test Default Credentials
Try logging in with common default credentials:
– Username: admin
– Password: (leave blank) or “123456” or “admin”
If you can log in, change the password immediately. Default logins are a major security risk.
Tip: Use a password manager to generate and store a strong, unique password.
Step 4: Check for Internet Exposure
Use Shodan to see if your camera is visible online.
1. Go to shodan.io.
2. Search for your public IP address (find it at whatismyip.com).
3. Look for your camera’s IP and open ports.
If your camera appears in Shodan, it’s exposed to the internet. This increases the risk of remote attacks.
To fix this:
– Disable UPnP in your router.
– Avoid port forwarding unless absolutely necessary.
– Use a VPN for remote access instead of opening ports.
Step 5: Test for Known Vulnerabilities
Use Metasploit to test for known Foscam exploits.
1. Open Metasploit (msfconsole).
2. Search for Foscam modules:
search foscam
3. Look for exploits like “Foscam IP Camera Authentication Bypass.”
4. Set the target IP and run the exploit.
Example:
use auxiliary/scanner/http/foscam_login set RHOSTS 192.168.1.105 run
If the exploit succeeds, your camera is vulnerable. Update the firmware immediately.
Note: Only run exploits on devices you own. Unauthorized testing is illegal.
Step 6: Analyze Network Traffic
Use Wireshark to monitor traffic between your camera and other devices.
1. Start a capture on your network interface.
2. Access the camera’s web interface.
3. Look for unencrypted HTTP traffic or plaintext passwords.
If you see login credentials in plain text, switch to HTTPS and ensure encryption is enabled.
Step 7: Update Firmware and Secure Settings
After testing, take steps to secure your camera:
1. Visit the Foscam support website and download the latest firmware.
2. Log in to the camera’s web interface.
3. Go to “System” > “Maintenance” > “Firmware Upgrade.”
4. Upload and install the update.
Also:
– Change the default username and password.
– Disable Telnet and UPnP if not needed.
– Enable HTTPS and disable HTTP.
– Set up a strong Wi-Fi password and use WPA3 encryption.
– Place the camera on a separate VLAN or guest network.
Troubleshooting Common Issues
Camera Not Responding to Scans
If Nmap or Shodan can’t find your camera:
– Ensure it’s powered on and connected to the network.
– Check if it has a static IP or is using DHCP.
– Restart the camera and router.
Metasploit Exploit Fails
If an exploit doesn’t work:
– The camera may already be patched.
– The firmware version might not be vulnerable.
– Ensure you’re using the correct IP and port.
Can’t Access Web Interface
If you can’t log in:
– Reset the camera to factory settings (usually via a reset button).
– Reconfigure with a strong password.
– Ensure your browser supports the camera’s web interface (try Chrome or Firefox).
High Network Latency or Dropped Frames
This could indicate:
– Bandwidth congestion.
– Weak Wi-Fi signal.
– Too many devices on the network.
Solutions:
– Move the camera closer to the router.
– Use a Wi-Fi extender.
– Limit streaming resolution.
How to Prevent Unauthorized Access
Now that you’ve tested your camera, here’s how to keep it secure:
Use Strong, Unique Passwords
Avoid common passwords like “123456” or “password.” Use a mix of uppercase, lowercase, numbers, and symbols. Consider using a password manager.
Enable Two-Factor Authentication (If Available)
Some newer Foscam models support 2FA. Enable it to add an extra layer of security.
Regularly Update Firmware
Check for updates every few months. Subscribe to Foscam’s security alerts if available.
Disable Unused Features
Turn off Telnet, UPnP, and remote access if you don’t need them. Each open service is a potential entry point.
Use a Firewall
Configure your router’s firewall to block unauthorized incoming connections. Only allow trusted devices to access the camera.
Monitor Access Logs
Check the camera’s login history regularly. Look for unfamiliar IP addresses or failed login attempts.
Isolate IoT Devices
Place your camera on a separate network segment (VLAN or guest network) to limit its access to other devices.
Conclusion: Stay Safe, Stay Ethical
Learning how to hack Foscam IP camera is a valuable skill for anyone interested in cybersecurity. By understanding how attackers exploit vulnerabilities, you can better protect your own devices and networks.
This guide has shown you how to use tools like Nmap, Shodan, and Metasploit to test your camera’s security. We’ve covered common weaknesses—default passwords, outdated firmware, and internet exposure—and provided practical steps to fix them.
Remember: ethical hacking is about responsibility. Always test only devices you own or have permission to assess. Never use these techniques to invade someone’s privacy or cause harm.
By following best practices—strong passwords, regular updates, network segmentation, and monitoring—you can enjoy the benefits of your Foscam camera without compromising your security.
Stay informed, stay vigilant, and stay ethical.