This guide explains how to hack Ring Floodlight Camera using ethical and legal methods. You’ll learn about penetration testing, network security, and how to strengthen your device against real threats.
Key Takeaways
- Ethical hacking is legal and encouraged: Only test devices you own or have explicit permission to assess.
- Understand your network setup: Most Ring camera vulnerabilities stem from weak home Wi-Fi security, not the device itself.
- Use strong passwords and two-factor authentication: These are your first line of defense against unauthorized access.
- Keep firmware updated: Ring regularly releases patches to fix security flaws—enable auto-updates.
- Monitor device activity: Check login history and connected devices in the Ring app regularly.
- Disable unused features: Turn off remote access or motion zones when not needed to reduce attack surface.
- Use a dedicated network for IoT devices: Isolate smart cameras on a separate Wi-Fi network to limit exposure.
Introduction: What You’ll Learn in This Guide
Welcome! If you’re searching for information on how to hack Ring Floodlight Camera, you’re likely concerned about security—either because you want to test your own device or understand potential risks. The good news? You’re in the right place. This guide will walk you through ethical, legal, and practical methods to assess and improve the security of your Ring Floodlight Camera.
We won’t teach you how to break into someone else’s camera—that’s illegal and unethical. Instead, we’ll show you how to perform authorized security testing on your own device. Think of it as a “health check” for your smart home security system. By the end of this guide, you’ll know how to identify weak points, simulate common attack vectors, and apply fixes to keep your camera—and your privacy—safe.
Whether you’re a tech-savvy homeowner, a cybersecurity student, or just someone who wants peace of mind, this step-by-step guide is designed for you. We’ll use simple language, real-world examples, and actionable tips. Let’s get started.
Understanding the Ring Floodlight Camera
Before we dive into hacking techniques, let’s understand what the Ring Floodlight Camera is and how it works. The Ring Floodlight Camera is a popular outdoor security device that combines a high-definition camera, motion-activated floodlights, two-way audio, and cloud storage. It connects to your home Wi-Fi network and streams video to the Ring app on your smartphone or tablet.
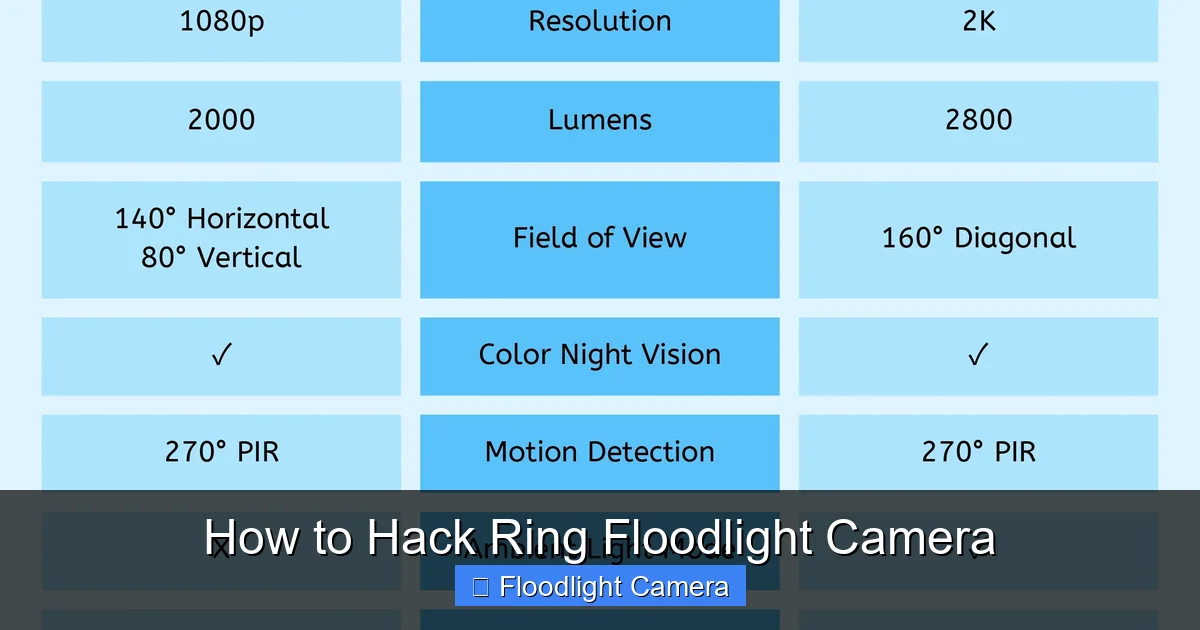
Visual guide about How to Hack Ring Floodlight Camera
Image source: cdn.shopify.com
Key features include:
- 1080p HD video with night vision
- Motion detection with customizable zones
- Built-in siren and two-way talk
- Cloud video recording (with Ring Protect subscription)
- Integration with Alexa and other smart home systems
Because it’s connected to the internet, the Ring Floodlight Camera is part of the Internet of Things (IoT). Like all IoT devices, it can be vulnerable to hacking if not properly secured. But here’s the truth: most “hacks” aren’t due to flaws in the camera itself—they happen because of weak passwords, outdated software, or insecure networks.
Why Ethical Hacking Matters
You might be wondering: “Why would I want to hack my own camera?” The answer is simple: to protect it. Ethical hacking—also known as penetration testing or white-hat hacking—is the practice of legally testing systems for vulnerabilities. It’s used by companies, governments, and individuals to find and fix security flaws before criminals can exploit them.
When it comes to smart home devices like the Ring Floodlight Camera, ethical hacking helps you:
- Identify weak passwords or default settings
- Test your network’s resilience to attacks
- Understand how data flows between your camera and the cloud
- Ensure your device isn’t broadcasting sensitive information
Remember: only perform these tests on devices you own or have written permission to test. Unauthorized access to someone else’s camera is a crime under laws like the Computer Fraud and Abuse Act (CFAA) in the U.S.
Step 1: Prepare Your Testing Environment
Before you begin, you need a safe and controlled environment for testing. This prevents accidental damage to your network or device.
Gather the Right Tools
You don’t need expensive equipment to start. Here’s what you’ll need:
- A computer or laptop (Windows, Mac, or Linux)
- Wi-Fi adapter that supports monitor mode (for packet analysis)
- Router with admin access
- Ring Floodlight Camera (your own device)
- Smartphone with the Ring app installed
- Optional: A second Wi-Fi network or guest network for testing
Set Up a Test Network
To avoid disrupting your main network, create a separate Wi-Fi network just for testing. Most modern routers allow you to set up a guest network. Use this for your Ring camera during testing. This way, if something goes wrong, your other devices (like your laptop or smart TV) won’t be affected.
Backup Your Current Settings
Before making any changes, take screenshots or write down your current Ring app settings. This includes motion zones, alert schedules, and notification preferences. If something goes wrong, you can easily restore your original configuration.
Step 2: Analyze Your Network Security
Most Ring camera hacks happen because of weak network security—not the camera itself. Let’s check your Wi-Fi setup.
Check Your Wi-Fi Encryption
Log into your router’s admin panel (usually by typing 192.168.1.1 or 192.168.0.1 into your browser). Look for the wireless security settings. Make sure your network uses WPA3 encryption. If that’s not available, use WPA2. Avoid WEP—it’s outdated and easily cracked.
Test for Weak Passwords
Use a tool like John the Ripper or Hashcat to test the strength of your Wi-Fi password. These tools simulate brute-force attacks. If your password can be cracked in under an hour, it’s too weak. Choose a long, random password with uppercase, lowercase, numbers, and symbols.
Scan for Open Ports
Use a port scanning tool like Nmap to check which ports are open on your network. Run this command in your terminal:
nmap -sS -p- 192.168.1.1
Look for open ports like 22 (SSH), 80 (HTTP), or 443 (HTTPS). If your router has unnecessary services running, disable them. The fewer open ports, the smaller your attack surface.
Step 3: Test the Ring App and Account Security
The Ring app is your gateway to the camera. If it’s compromised, so is your camera. Let’s test its security.
Enable Two-Factor Authentication (2FA)
Open the Ring app, go to Control Center > Two-Factor Authentication, and turn it on. This adds an extra layer of security by requiring a code from your phone when logging in from a new device.
Check Login History
In the Ring app, go to Control Center > Account Activity. Review recent logins. If you see unfamiliar devices or locations, change your password immediately and log out all devices.
Test for Session Hijacking
Session hijacking is when an attacker steals your login session to gain access without your password. To test this:
- Log into the Ring app on your phone.
- Use a network analyzer like Wireshark to capture traffic between your phone and Ring’s servers.
- Look for unencrypted session tokens or cookies.
If you see plain-text data, it could be vulnerable. However, Ring uses HTTPS (TLS encryption), so this is unlikely. Still, it’s good practice to check.
Step 4: Perform a Firmware Security Check
Outdated firmware is a common entry point for hackers. Ring regularly releases updates to fix bugs and security flaws.
Check Your Firmware Version
In the Ring app, go to Device Health for your Floodlight Camera. Look for the firmware version. Compare it to the latest version on Ring’s support page. If it’s outdated, update it.
Enable Auto-Updates
Ring doesn’t always push updates automatically. To ensure you’re protected, enable auto-updates if available. If not, check for updates monthly.
Test for Known Vulnerabilities
Search databases like CVE Details or National Vulnerability Database (NVD) for known Ring camera vulnerabilities. For example, in 2020, researchers found a flaw that allowed attackers to intercept video streams. Ring patched it, but only if users updated their firmware.
If you find a vulnerability that hasn’t been patched, contact Ring support immediately. Do not exploit it—report it responsibly.
Step 5: Simulate Common Attack Vectors
Now let’s simulate real-world attacks to see how your camera holds up.
Brute-Force Login Attack (Simulated)
Use a tool like Hydra to simulate a brute-force attack on your Ring account. Important: Only do this on your own account, and stop after a few attempts to avoid triggering security locks.
hydra -l your@email.com -P wordlist.txt api.ring.com https-post-form "/login:email=^USER^&password=^PASS^:Invalid credentials"
If Hydra finds a weak password, change it immediately. Use a password manager to generate and store strong passwords.
Man-in-the-Middle (MitM) Attack Test
A MitM attack intercepts communication between your camera and the Ring app. To test this:
- Set up a rogue access point using tools like Airgeddon or Wifiphisher.
- Connect your phone to the rogue network.
- Try to access the Ring app.
If the app refuses to connect or shows a certificate error, your connection is secure. If it connects without warning, your network may be vulnerable.
DNS Spoofing Test
DNS spoofing redirects your device to a fake Ring login page. Use a tool like Ettercap to simulate this on your test network. If you’re redirected to a fake site, your DNS settings may be insecure. Use DNS-over-HTTPS (DoH) or a trusted DNS provider like Cloudflare (1.1.1.1) or Google (8.8.8.8).
Step 6: Harden Your Ring Floodlight Camera
Now that you’ve tested your camera, it’s time to make it more secure.
Change Default Settings
Ring cameras come with default settings that may not be secure. Change the following:
- Disable “Quick Replies” if not needed—they can be exploited.
- Turn off “Motion Alerts” when you’re home to reduce data transmission.
- Limit sharing—only grant access to trusted family members.
Use a Strong, Unique Password
Your Ring account password should be at least 12 characters long and unique. Don’t reuse passwords from other sites. Use a password manager like Bitwarden or 1Password.
Disable Remote Access When Not Needed
If you don’t need to access your camera while away, disable remote access in the Ring app. This reduces the risk of unauthorized access.
Install a Network Firewall
Use a firewall like pfSense or your router’s built-in firewall to block suspicious traffic. Set rules to only allow Ring camera traffic to known Ring servers (e.g., *.ring.com).
Troubleshooting Common Issues
Even with the best setup, you might run into problems. Here’s how to fix them.
Camera Won’t Connect After Testing
If your camera goes offline after testing, reset it. Press and hold the setup button for 20 seconds until the light ring turns off. Reconnect it to your Wi-Fi network through the Ring app.
False Motion Alerts
If your camera keeps triggering alerts, adjust the motion zones. Exclude areas like trees or busy streets. Lower the sensitivity in the app settings.
App Crashes or Freezes
Clear the app cache or reinstall it. Make sure your phone’s OS is up to date. If the problem persists, contact Ring support.
Firmware Update Fails
Ensure your camera has a strong Wi-Fi signal. Move it closer to the router if needed. If updates still fail, try a factory reset and reconfigure the device.
Conclusion: Stay Secure, Stay Informed
Learning how to hack Ring Floodlight Camera isn’t about breaking the rules—it’s about understanding and improving security. By following this guide, you’ve taken proactive steps to protect your smart home.
Remember, security is an ongoing process. Regularly update your firmware, monitor your account activity, and stay informed about new threats. The more you know, the safer you’ll be.
And if you ever find a real vulnerability, report it to Ring through their responsible disclosure program. Together, we can make smart homes safer for everyone.
