As we continue to shift towards a more digitally-driven era, surveillance has become a more prevalent topic of discussion. With more and more data circulating, the need to monitor and protect oneself has never been greater. This leads to the question, what are the different types of surveillance? Surveillance can generally be categorized into two types – physical and digital.
Physical surveillance involves the monitoring of a person’s behaviour through direct observation, whereas digital surveillance involves the tracking and gathering of data through electronic devices. Physical surveillance can be conducted through various means such as CCTV, drones, GPS tracking, and wiretapping. These methods are often utilized by law enforcement agencies, private investigators, and even by individuals for their own personal security.
On the other hand, digital surveillance can be conducted through online monitoring, social media tracking, and even the use of cookies on websites. As our online presence increases, so does the amount of data that can be collected about us. This information can be used for targeted advertising, as well as more nefarious activities such as identity theft.
In conclusion, surveillance is a broad topic that can be approached from many different angles. Understanding the different types of surveillance is crucial in order to protect ourselves and our privacy in a world where data is constantly being collected.
Visual Surveillance
When it comes to surveillance, there are many types, each with its own unique purpose and application. One of the most common forms of surveillance is visual surveillance, which can be done through cameras, drones, or even satellites. Visual surveillance can be used for a variety of reasons, such as monitoring public spaces for safety purposes, ensuring compliance with regulations, or even investigating criminal activity.
With advancements in technology, visual surveillance has become more sophisticated, allowing for higher resolution images, facial recognition, and even night vision capabilities. However, it’s important to balance the benefits of visual surveillance with concerns about privacy and potential misuse. As surveillance technology continues to evolve, it’s important for individuals and organizations to stay informed and aware of its uses and limitations.
CCTV cameras, drones
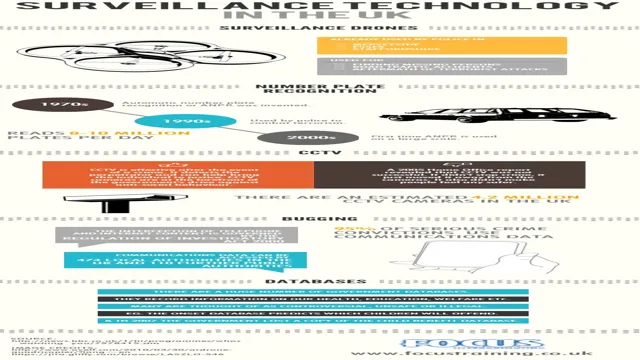
Visual surveillance has become much easier with the advent of CCTV cameras and drones. These technologies have been used extensively by law enforcement agencies to monitor public spaces and track criminal activities. CCTV cameras are installed in various locations such as shopping malls, streets, and even public transportation hubs to capture video footage of any suspicious activity.
On the other hand, drones are used to capture aerial views of areas that are difficult to access. With these technologies in place, it has become much easier for authorities to keep a watchful eye on the general public and track down troublemakers. However, the use of visual surveillance has also raised concerns about privacy violations.
While it is important to ensure public safety, it is equally important to protect the privacy of individuals. As such, strict regulations need to be implemented to ensure that the use of these technologies does not infringe on human rights. In summary, the use of CCTV cameras and drones in visual surveillance has brought many benefits, but it is essential to carefully balance their use with privacy protection.

License plate readers
License plate readers are a type of visual surveillance technology that captures images of vehicles and their license plates in real-time. These readers are often used by law enforcement agencies to track traffic violations, investigate crimes, and locate stolen vehicles. The technology works by using cameras and optical character recognition software to capture and process images of license plates, which are then checked against databases of registered vehicles and criminal records.
License plate readers can be mounted on stationary structures like poles and buildings or placed on vehicles like police cars. While license plate readers can be an effective tool for law enforcement, they also raise concerns about privacy and surveillance. Some worry that the technology could be abused for mass surveillance or used to track the movements of innocent people.
As such, there are debates about regulating the use of license plate readers and implementing proper safeguards to protect individual privacy.
Audio Surveillance
There are many types of surveillance techniques utilized in recent times, and one of them is audio surveillance. This technique involves recording sounds without anyone being aware of it. There are various types of audio surveillance techniques available, such as wiretapping, hidden microphones, and bugs.
These tools can be used in different settings to gather information on targeted individuals or groups. Wiretapping is a type of audio surveillance that involves intercepting telephone conversations, whereas hidden microphones and bugs are used to record conversations in-person or in a particular location. These techniques can raise privacy concerns, and in many cases, their use is restricted by law.
However, in certain cases, such as law enforcement investigations, audio surveillance can be a useful tool to gather critical evidence. Overall, audio surveillance is just one of many types of surveillance techniques that are used today to monitor and record people’s activities.
Wiretapping, hidden microphones
Audio Surveillance technology has come a long way since the first wiretapping and hidden microphone devices were invented. Nowadays, audio surveillance can be carried out using a wide variety of sophisticated equipment, ranging from high-quality microphones to advanced digital recorders and even specialized software programs. In fact, audio surveillance has become so advanced that it is now possible to monitor a conversation from a remote location in real-time, using nothing more than an internet connection and a simple device.
However, despite the advancements in technology, audio surveillance is still a controversial topic, with many people expressing concerns about the potential for unauthorized eavesdropping and invasion of privacy. As a result, it is important for individuals and organizations to be aware of the legal and ethical implications of using audio surveillance technology and to use it responsibly and in accordance with the law. At the same time, it is also important to recognize the many benefits that audio surveillance can offer, from improving workplace productivity to enhancing security and safety in public spaces.
By embracing these benefits while also respecting the privacy and rights of others, we can create a more secure and prosperous society for all.
Physical Surveillance
When it comes to surveillance, there are various types of techniques and technologies employed to monitor people. One of these techniques is physical surveillance. Physical surveillance involves the use of humans rather than technology to monitor individuals.
This technique can range from undercover officers staking out a location to discreetly gathering information on people, to employees watching out for theft in a retail store. One of the benefits of physical surveillance is that it can provide insight into the actual behavior of a person, which can be important in certain situations. However, it is important to note that physical surveillance can be intrusive and sometimes illegal if not conducted in compliance with the law.
Overall, it is important to be aware of the various types of surveillance that exist and to understand the implications of each.
Stalking, following, tracking devices
Physical Surveillance Physical surveillance involves the use of stalking, following, or tracking devices to keep tabs on someone’s location, activities, and movements. While this type of surveillance is often used by law enforcement in investigations, it can also be utilized by individuals or groups for personal reasons. Stalking, in particular, is a serious crime that can cause emotional distress and put the victim’s safety at risk.
It’s important to be aware of the signs of physical surveillance, such as noticing someone following you or repeatedly seeing the same person in different locations. If you suspect that you’re being physically surveilled, it’s important to report it to the authorities and take steps to increase your personal security. This may include varying your routine, avoiding certain areas, or investing in personal security devices.
With the rise of technology, it’s important to also be aware of the potential use of tracking devices, such as GPS, in personal and professional settings. Overall, physical surveillance can be a serious violation of personal privacy and safety, and it’s important to take steps to protect yourself if you suspect you’re being targeted.
Internet Surveillance
It’s no secret that internet surveillance is a hotly debated topic, and for good reason. There are several types of surveillance that users need to be aware of. The most common type of surveillance is data surveillance, where data is intercepted and inspected to determine if a user presents a threat or is involved in illegal activities.
Another type of surveillance is content surveillance, where the actual content of messages or emails is monitored. Then, there is physical surveillance where activity is tracked through mobile devices or GPS. Social media surveillance is also rampant, whereby user activity is monitored on social media platforms to collect data for targeted advertising purposes.
Finally, there is behavioral surveillance, where user behavior is monitored on websites and apps to create profiles for targeted advertising. It’s important to understand the different types of surveillance and take steps to protect your online privacy, such as using a VPN or anti-tracking tools.
Email monitoring, social media tracking
In today’s digital age, internet surveillance is a necessary precaution for individuals and businesses alike. Monitoring emails and tracking social media accounts can help detect potential threats and illegal activities. Email monitoring can detect suspicious or unauthorized access to sensitive information and prevent data breaches.
Social media tracking can help identify any online attacks on a brand’s reputation or potential leaks of confidential information. By keeping an eye on these channels, it is possible to ensure the safety and security of sensitive information, prevent fraud, and protect a brand’s reputation. With internet surveillance tools, online activities can be monitored, and suspicious behavior can be addressed before any harm is done.
As the internet continues to evolve, so must the ways in which we protect ourselves and our businesses. Internet surveillance is an essential tool for ensuring privacy and security in an increasingly interconnected world.
Browser tracking, keystroke logging
With the increasing use of the internet, we’ve grown accustomed to sharing personal information online. However, we might not realize that our browsing activities are being tracked by websites and third-party applications. Browser tracking is the process of collecting and analyzing data related to a user’s browsing behavior.
This data can be used to create a digital profile of the user, which can then be used to target specific ads or even sell to other companies. Moreover, some websites engage in keystroke logging, or the process of recording every keystroke we make on our computer. This includes passwords, usernames, and any other sensitive information we might input.
This information can be used for malicious purposes such as identity theft or fraud. It’s essential to remain cautious about the websites we visit and what personal information we share online to prevent any unwanted surveillance and protect our privacy.
Data Surveillance
When it comes to data surveillance, there are actually quite a few different types to consider. For starters, there is physical surveillance, which includes the use of cameras, tracking devices, and other methods of monitoring people in real life. Then, there is digital surveillance, which can include everything from monitoring internet activity to tracking someone’s location through their smartphone.
In addition to these more traditional forms of surveillance, there are also social media surveillance, financial surveillance, and even medical surveillance. Each of these types of surveillance has its own unique concerns and implications, and it’s important to be aware of them in order to protect your privacy. So, the next time you’re online or out in the world, keep in mind just how many different types of surveillance might be watching you.
Conclusion
In conclusion, the number of types of surveillance is almost as extensive as the list of excuses we come up with to avoid it. From physical to digital, overt to covert, and government to commercial, there are countless ways in which we can be monitored and observed. But don’t worry, it’s not all doom and gloom.
With awareness and education, we can actively protect our privacy and look out for our fellow citizens. So let’s keep our eyes and ears open, and never forget the power of a good old-fashioned tin foil hat.”
FAQs
What is physical surveillance?
Physical surveillance is the act of monitoring a person’s actions and movements in person or via video surveillance.
What is electronic surveillance?
Electronic surveillance involves monitoring a person’s online activities, including their internet usage, email, and phone activity, with or without their knowledge.
What is covert surveillance?
Covert surveillance is the practice of conducting surveillance without the subject’s knowledge or consent.
What is aerial surveillance?
Aerial surveillance involves using drones or planes to capture footage from above, commonly used for monitoring large areas or tracking movements of groups or individuals.
What is computer surveillance?
Computer surveillance involves using software to monitor a person’s computer usage, including keystrokes, internet activity, and file access.
What is biometric surveillance?
Biometric surveillance uses advanced technologies to identify individuals based on unique physical traits, such as DNA, iris scans, or facial recognition.