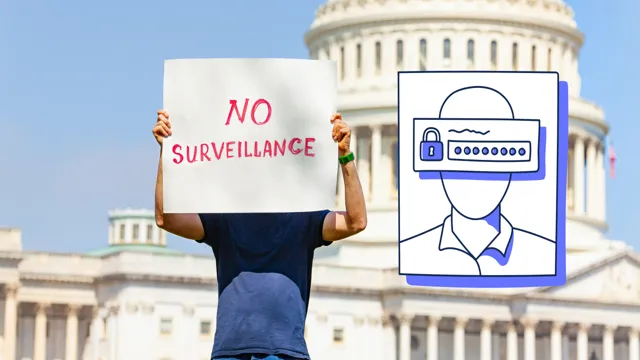
Surveillance has become a common part of our lives in recent years. We give up our personal data every time we use the internet or engage with technology, and sometimes we don’t even know it. The types of government surveillance have grown as technology advances, and with it, so have concerns over privacy.
It’s essential to be aware of the different ways governments can surveil citizens to better understand the potential implications. From monitoring phone calls and emails to tracking movements and biometric data, there are several types of government surveillance to consider. So, let’s take a deep dive into exploring these different forms of government surveillance and their impact on our lives.
Wiretapping
Types of government surveillance could involve wiretapping, which is the practice of intercepting telephone conversations by tapping into the physical phone line or accessing the network that the phone uses to communicate. Wiretapping is usually done by the government in order to monitor the communication of suspected criminals or terrorists. This type of surveillance can also be done on digital communication platforms such as email or instant messaging.
Although wiretapping is meant to protect national security, it has been a topic of controversy due to privacy concerns. The use of wiretapping has to be regulated and warrants must be obtained in order to prevent abuse of power. It is important for the government to balance between the need for security and the protection of individual privacy.
Phone conversations, emails, text messages
Wiretapping is a serious concern when it comes to phone conversations, emails, and text messages. It refers to the act of secretly intercepting and recording communication without the consent of the parties involved. Wiretapping is illegal and a violation of privacy rights.
With the advancement of technology, wiretapping has become more prevalent and sophisticated. Cybercriminals and government agencies can use various methods to intercept communication, including hacking into devices, installing spyware, or accessing networks. It is essential to take measures to protect your communication from wiretapping.
This includes using encryption methods, ensuring secure passwords, and being cautious when using public Wi-Fi networks. If you suspect that your communication has been wiretapped, it is crucial to report it to the proper authorities immediately. By being vigilant and taking precautions, you can protect your privacy and keep your communication secure.
Video Surveillance
When it comes to government surveillance, there are several different types that they can use to keep an eye on activities. One of the most common forms of surveillance is video surveillance, which involves monitoring activities through video cameras placed in public areas. This can include everything from monitoring traffic flow to watching for criminal activity.
Another type of government surveillance is electronic surveillance, which involves intercepting and monitoring electronic communications such as phone calls and emails. This type of surveillance is often used by law enforcement agencies to gather evidence in criminal cases. Finally, there is physical surveillance, which involves monitoring individuals in person by following them or watching them through binoculars or other devices.
While these different types of surveillance can be useful in certain situations, many people have concerns about privacy and civil liberties when it comes to government monitoring of their activities.
CCTV cameras, drones, satellites
Video Surveillance With the rise of technological advancements, video surveillance has taken on a new level of importance. CCTV cameras, drones, and satellites are all powerful tools used in video surveillance. These tools have revolutionized the way we monitor and track criminal activity.
CCTV cameras have become ubiquitous in public places, and they serve as a deterrent to crime. They have the ability to capture video footage of criminal activity, which can be used as evidence in court. Drones have the ability to fly over large areas, giving law enforcement a bird’s eye view of an area.
They can also zoom in on specific objects and provide high-quality video footage. Satellites are also used to monitor large areas, and they can capture video footage in places that are difficult to access. With video surveillance, law enforcement can quickly and efficiently monitor and respond to criminal activity, making our communities safer.
Internet Monitoring
As the internet continues to play an increasingly important role in our lives, governments around the world have been investing in a variety of tools to monitor users’ online activity. These can include everything from tracking the websites that people visit to intercepting their messages and tracking their physical movements. One type of government surveillance is known as “metadata collection,” which involves collecting information about the communication patterns between individuals rather than the content of their messages.
Another type is “content surveillance,” which involves intercepting actual messages or conversations. Finally, “mass surveillance” involves monitoring and collecting data on a large scale, without necessarily targeting specific individuals or groups. While governments argue that these measures are necessary for national security, there is growing concern among privacy advocates that they represent a violation of individual rights.
As we continue to navigate the digital age, it is important to remain aware of the ways in which our online activities are being monitored and to advocate for policies that protect our fundamental rights.
Web browsing, social media, online activity
Internet monitoring is becoming increasingly necessary in today’s world, where most of our social, personal, and business activities happen online. It involves tracking and monitoring an individual’s internet usage to ensure safety, productivity, and compliance with company policies. With internet monitoring software, employers can monitor employees’ web browsing, social media, and other online activities to ensure they are not wasting time on non-work related activities.
It also helps to protect the company’s confidential information by detecting any potential security threats, such as malware or phishing scams. Individuals can also benefit from internet monitoring to protect their online identity and personal information from hackers and other cyber threats. Overall, internet monitoring is a vital tool in ensuring online safety, security, productivity, and compliance, making it a crucial aspect of modern-day internet usage.
Location Tracking
One of the types of government surveillance that’s been widely debated in recent years is location tracking. This type of tracking allows the government to monitor the movements and whereabouts of individuals, which raises concerns about privacy and freedom. Location tracking can be done through various means, including cell tower triangulation, GPS tracking, and even the analysis of social media and other online activity.
Proponents of location tracking argue that it can be a useful tool for law enforcement in investigations and emergency situations, while opponents argue that it violates individual rights and can lead to abuse of power. Regardless of one’s stance, it’s important to keep the conversation going around this type of government surveillance and to explore ways to balance individual privacy with the needs of law enforcement.
GPS, cell towers, license plate scanners
If you own a smartphone, chances are you’re being tracked without even knowing it. GPS, cell towers, and license plate scanners are just a few of the methods used to track your location. GPS is the most common method, as it uses satellite signals to pinpoint your exact location.
But even if you turn off GPS, your phone can still be tracked using cell tower data. This is because your phone regularly pings nearby cell towers to maintain a connection to the network. License plate scanners are also becoming more popular for tracking vehicles.
These devices are usually mounted on police cars and can scan hundreds of plates per minute, cross-referencing them with a government database. While location tracking technology can be useful for finding lost phones or tracking vehicles, it also raises concerns about privacy and surveillance. As a user, it’s important to be aware of your privacy settings and to question whether you want to be tracked all the time.
Financial Monitoring
When it comes to financial monitoring, there are different types of government surveillance that one might encounter. One type is transaction monitoring, where financial transactions are analyzed for fraud, money laundering, or other suspicious activity. Another type is social network analysis, where relationships between individuals and their financial activities are observed to uncover potential criminal activity.
Additionally, some governments may monitor digital currency exchanges or online marketplaces for illicit trade. All of these surveillance methods aim to keep financial systems safe and protect against illegal activities. However, there is often a balance between security and privacy concerns, and it is important for governments to uphold the rights of individuals while maintaining a secure financial system.
Bank accounts, credit card transactions, money transfers
Financial monitoring is a crucial aspect of managing personal or business finances. It involves the tracking and analysis of bank account activities, credit card transactions, and money transfers. By monitoring financial activities, you can keep track of your expenses, identify areas where you can cut costs, and detect any fraudulent or suspicious transactions.
This is particularly important for businesses, where financial monitoring can help prevent financial losses caused by embezzlement or internal fraud. With the help of modern technologies such as AI-powered financial software, monitoring your finances has become easier and more efficient. Regular financial monitoring can help you stay on track with your financial goals and make informed decisions based on your financial data.
It’s important to note that financial monitoring should not be done in isolation, but rather as part of a broader financial management plan. By keeping tabs on your financial activities, you can improve your financial health and achieve financial stability and security.
Conclusion
After examining the different types of government surveillance, it’s clear that our privacy is more fragile than we might think. From the classic spy movies to the modern-day techniques of data mining and social media analysis, governments have the power to gather information on us far beyond what we ever intended to share. While some may argue that this is for our own safety, we must also acknowledge the potential for abuse and infringement on our basic rights.
Ultimately, it’s up to us as citizens to stay informed and demand accountability from our leaders to ensure that our privacy remains protected. As the old saying goes, “If you’re not doing anything wrong, you have nothing to hide” – but who gets to decide what’s “wrong”?”
FAQs
What is government surveillance?
Government surveillance refers to the monitoring and observation of individuals or groups by the government or its agencies.
What are the different types of government surveillance?
There are several types of government surveillance, including physical surveillance, electronic surveillance, and data surveillance.
What is physical surveillance?
Physical surveillance involves monitoring someone in person, such as through the use of cameras, microphones, or other tracking devices.
What is electronic surveillance?
Electronic surveillance involves monitoring someone’s electronic communications, such as phone calls, emails, or social media activity.
What is data surveillance?
Data surveillance involves the collection and analysis of large amounts of data to identify patterns of behavior, such as through the use of facial recognition technology or machine learning algorithms.
